Overview
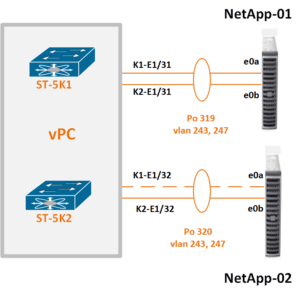
I was recently troubleshooting a vPC port channel issue with a pair of Nexus 5500 switches that were trying to implement new port channels to two NetApp controllers.
I got involved when my storage friend sent me an email one evening asking me to check the port channel for one interface that was not wanting to participate in the port channel from the NetApp perspective. As it turned out, I was not initially able to contact him for more details because we were working different shifts.
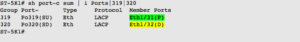
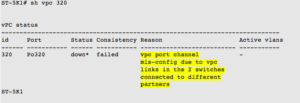
I checked on the N5Ks, and I saw that one port channel was down on ST-5K1, but all of the other port channels were up.
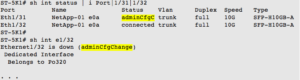
I checked the physical interface status for the port channel, and the interface for the down port channel appeared not to be connected.
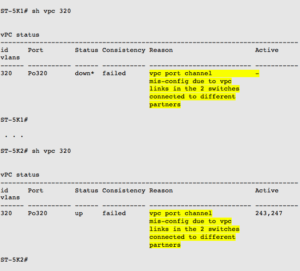
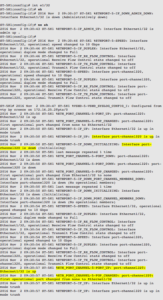
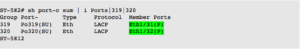
The vPC results showed that the ST-5Ks thought two different devices were connected to their respective e1/32 interfaces:
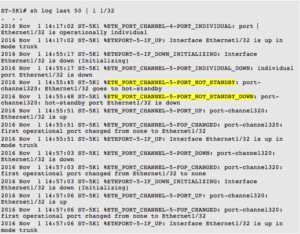
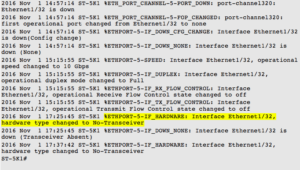
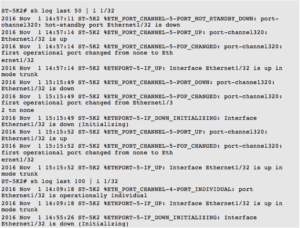
I checked the recent log messages for the interface. Maybe someone had pulled out the SFP?
Hmm — both 5Ks had complained about a hot standby state at the same time. I usually find this means the cables have been cross connected so the vPC port channel from the Nexus switch pair is connected to two different devices, which is not a supported state.
I was also wondering why the ST-5K1 17:25:45 log entry said the hardware type changed to No-Transceiver. This seemed off — I thought all the cables had been placed earlier. My guess was that no one had removed the SFP, and that maybe NX-OS was confused about the current state of the cables.
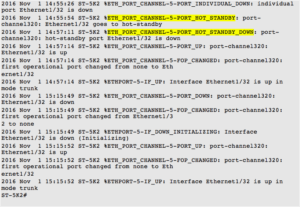
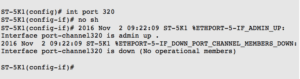
To see if I could clear out the ‘vpc port channel mis-config,’ I bounced the port channel interface.
I checked, and the vPC was still listed as misconfigured.
In addition, the physical interface had a new weird state:
I do not recall ever seeing a physical interface down due to adminCfgChange as the reason. But I interpreted the state to mean the NX-OS was confused about the interface state based on the configuration changes, so I also shut/no shut the physical interface e1/32.
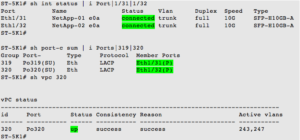
There were a lot of messages over the next 30 seconds or so. After all the initialization, both the interface and the port channel came up.
I sent a note to the storage team and they did confirm the port channels were now appearing correctly.
SUMMARY
My guess was the NX-OS on ST-5K1 was confused about the vPC port channel configuration due to cables that were incorrectly connected to two devices, then hot-swapped to the correct orientation. ST-5K1 appears to have needed the physical interface to be reset for the incorrect vPC port channel configuration to get cleared out. Possibly based on the timing or order of the cable swaps, ST-5K2 recovered on its own.